The Claude Computer Use API lets developers run secure, local commands and access files from Claude models, enabling robust custom workflows for software integration and autonomous agent development. This post provides a practical playbook for building local integrations with Claude, drawing on Anthropic developer tools and techniques like coding with Claude Dispatch.
What this post covers:
1. Why the Claude Computer Use API matters for local integrations
2. Background on Anthropic developer tools and Claude Dispatch
3. Current trends in autonomous agent development and software integration
4. A step-by-step playbook for building secure, maintainable local integrations
5. Forecasts and best practices to future-proof your integrations
3-step quick setup (featured-snippet friendly)
1. Install and authenticate the Claude Computer Use API client.
2. Define a minimal, sandboxed command surface and file access policy.
3. Test with a safe agent workflow (validate outputs and add retry/error handling).
For reference and deeper technical context, see the Claude Dispatch and Computer Use overview and related Anthropic developer tools documentation (https://claude.com/blog/dispatch-and-computer-use, https://docs.anthropic.com/).
Background
What the Claude Computer Use API is
The Claude Computer Use API is a controlled bridge between Claude models and a developer’s local environment. It exposes a narrowly defined runtime surface that lets models request local actions—running commands, reading or writing files, and launching short-lived processes—while enforcing security, observability, and auditable policies. Unlike a generic remote execution layer, this API is explicitly designed for model-driven side effects: the model can propose actions in natural language or structured form, and the runtime executes those actions under strict constraints.
This capability complements other Anthropic developer tools such as model endpoints and Dispatch: where endpoints answer queries and Dispatch orchestrates decisioning and routing, the Claude Computer Use API handles concrete, local side effects that must remain in your environment for compliance, latency, or data-locality reasons source: Claude Dispatch and Computer Use documentation.
Key components and concepts
- Authentication & credentials: Implement short-lived tokens and role-limited credentials. Use least-privilege principles and rotate tokens frequently.
- Command and file policies: Define whitelists for allowed binaries, sandboxed interpreters, and read-only vs read/write boundaries for file paths.
- Sandboxing and monitoring: Capture stdout/stderr, set CPU/memory/time limits, and enforce network egress restrictions. Provide audit logs for every invocation.
- Structured outputs: Prefer model responses that map to JSON schemas so downstream systems can validate and safely apply changes.
An analogy: treat the Claude Computer Use API like a locked toolbox the model can request tools from—your guardrails determine which tools it can use, and telemetry records which tool was pulled and why.
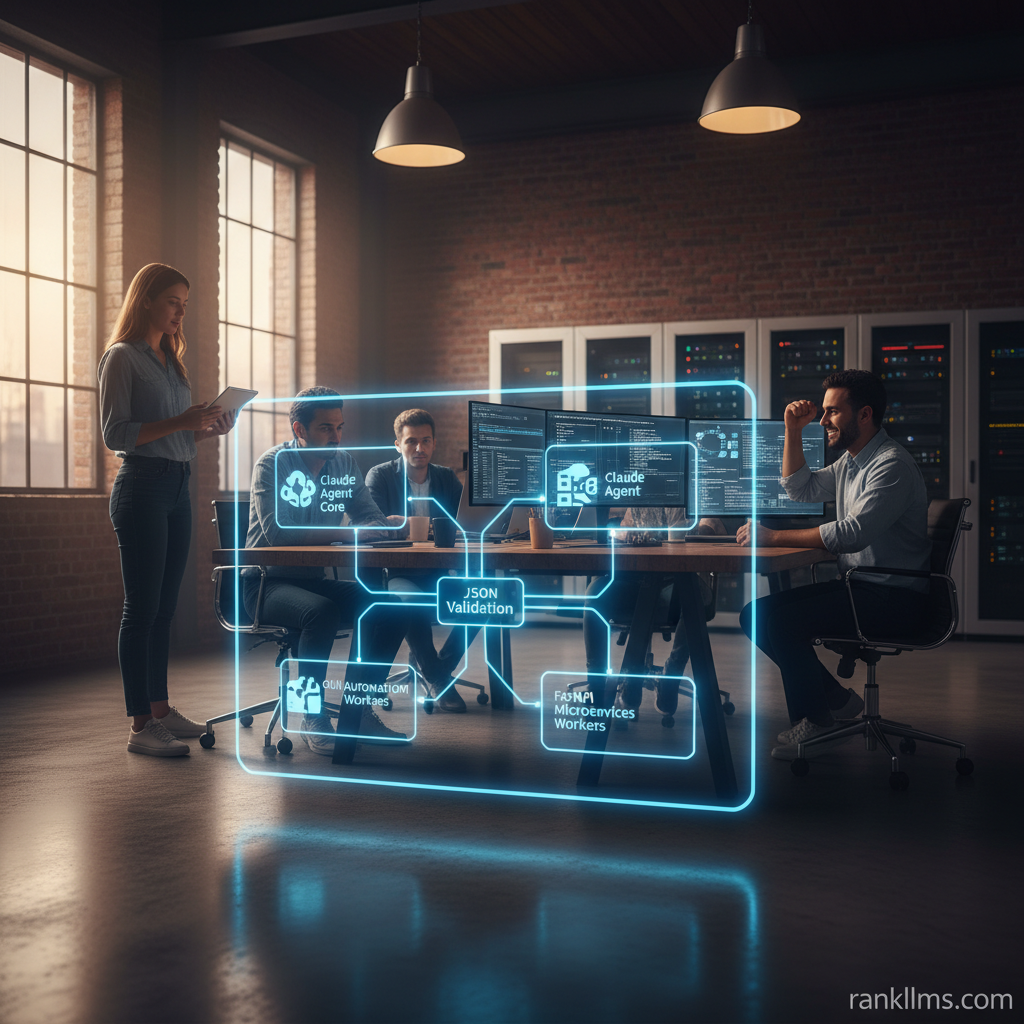
How it differs from and integrates with Claude Dispatch
Claude Dispatch is an orchestration layer for routing tasks across models, services, and microservices; it’s optimized for higher-level logic and decision flows. The preferred integration pattern is:
- Dispatch performs intent classification, subtasking, and produces structured action plans.
- The Claude Computer Use API executes the concrete, local operations that those plans require—file transforms, test runs, or CI hooks.
This separation keeps reasoning isolated from execution, reducing blast radius and improving observability. For practical details on this pairing and recommended patterns, see the Dispatch and Computer Use guide (https://claude.com/blog/dispatch-and-computer-use).
Trend
Why local integrations are surging
Several forces are driving adoption of local model execution surfaces like the Claude Computer Use API:
- Privacy and data locality: Enterprises process sensitive PII, financial records, or proprietary models on-prem or inside private VPCs to meet compliance.
- Autonomous agent development: Agents require controlled action capabilities—file edits, system calls, or orchestration hooks—to perform genuine automation tasks.
- Convergence of LLM orchestration and systems automation: Teams now expect models to produce reasoning that becomes deterministic system actions; bridging that gap requires secure, auditable local execution.
Organizations view the Computer Use API as a way to capture the benefits of advanced language models while maintaining operational control over side effects.
Common use cases driving adoption
- Automated developer tooling: generate code, run localized linters, run unit tests, and open pull requests via CI hooks.
- Secure data processing pipelines: execute transformations locally to avoid sending sensitive data to external APIs.
- Agent-enabled operations: scheduled maintenance tasks, incident remediation playbooks, or telemetry extraction performed autonomously but auditable.
Implementation patterns to watch
- Minimal-surface APIs: expose only the exact commands and file paths agents need; avoid generic shell access.
- Observability-first integrations: generate structured audit events, retain normalized outputs, and attach idempotency keys for retried actions.
- Hybrid architectures: use cloud-hosted models for reasoning plus localized execution via the Computer Use API for compliance-sensitive actions.
These trends reflect a broader industry shift toward hybrid model architectures where \”reason in the cloud, act locally\” becomes the standard approach.
Insight
Playbook: Building a production-ready local integration with Claude Computer Use API
1. Design & security
- Define a narrow purpose and document the threat model. Who can instruct the model? What files can be affected?
- Create explicit command/file whitelists; prefer read-only access when possible. Apply capability manifests to agents so permissions are explicit.
- Use short-lived tokens, mutual TLS (if available), and credential rotation. Store secrets in a dedicated secrets manager.
2. Developer ergonomics
- Build thin SDK wrappers (TypeScript, Python) that encapsulate the Computer Use API patterns—command invocation, stdout/stderr normalization, and schema validation.
- Provide helper functions and typed interfaces to reduce friction when coding with Claude Dispatch and for teams building agents.
- Document example prompts and recommended structured responses so model outputs are easier to parse and validate.
3. Orchestration and collaboration
- Use coding with Claude Dispatch for task decomposition and routing. Have Dispatch output a structured action plan (JSON) that maps directly to Computer Use API calls.
- Example: Dispatch decides \”generate unit tests for repo X\” and outputs steps with file paths and commands. The Computer Use API executes each step under policy controls.
4. Reliability & validation
- Validate model outputs against JSON Schema before applying stateful changes. Reject or sandbox unexpected shapes.
- Implement retries with idempotency keys, deterministic backoff, and clear error categories (transient vs fatal).
- Run canary commands in a sandbox before exposing to production.
5. Observability & auditing
- Capture inputs (sanitized), normalized outputs, exit codes, and runtime metadata. Store audit logs in an append-only store and surface dashboards for incidents.
- Correlate logs with Dispatch traces so you can reconstruct decision-to-action flows end-to-end.
6. Example checklist (developer-friendly)
- [ ] Authenticate client and verify permissions
- [ ] Start with a canary command in a sandbox
- [ ] Add schema validation for outputs
- [ ] Add logging, timeouts, and limits
- [ ] Review with security and ops teams
Short sample workflow (conceptual)
1. Dispatch decides an action (e.g., \”generate unit tests for repo X\”).
2. Dispatch generates a structured plan with steps and a target file path.
3. Claude Computer Use API executes a sandboxed script to run tests and write files.
4. System validates results, commits changes via a CI hook, and logs the run for audit.
For templates and orchestration patterns, consult Anthropic developer tools and Dispatch documentation (https://claude.com/blog/dispatch-and-computer-use, https://docs.anthropic.com/).
Forecast
What to expect next for Claude Computer Use API and related tools
- Higher-level SDKs and templates: Expect libraries that encapsulate common capability manifests and secure execution patterns, accelerating adoption across teams.
- Standardized safety primitives: Policy-as-code and policy registries for common scenarios (CI, data ingestion, backup) will emerge, making enforcement repeatable.
- Deep integration with autonomous agent frameworks: Agents will ship with curated capability manifests that map directly to Computer Use API surfaces, simplifying permissioning and audits.
- Enterprise adoption for hybrid architectures: More vendors will deliver managed orchestration layers that pair cloud reasoning with localized execution for compliance-sensitive workloads.
How to future-proof your integration
- Favor modular, policy-driven designs: Implement capability manifests so you can tighten or expand surfaces without a full rewrite.
- Invest in observability and automated tests: unit tests for SDKs, integration tests for workflows, and regular security scans.
- Monitor developments in coding with Claude Dispatch and Anthropic developer tools; adopt new orchestration primitives as they stabilize.
- Plan for policy evolution: keep your threat model and policies under version control and apply automated policy checks during CI.
Future implication: as safety primitives standardize and SDKs mature, teams will move faster from prototype to production while maintaining auditability and compliance. The combined momentum of autonomous agent development and hybrid architectures will make the Claude Computer Use API a core building block for secure, local automation.
CTA
Try a minimal integration today:
- Create a sandbox repo with a single, safe Computer Use API command (e.g., run linting on a small sample project).
- Pair that workflow with a Dispatch-driven plan so you can iterate on the action plan → execution loop.
Resources to get started:
- Claude Dispatch and Computer Use guide: https://claude.com/blog/dispatch-and-computer-use
- Anthropic developer tools docs and SDK references: https://docs.anthropic.com/
- Use JSON Schema validation for all model-generated outputs to prevent accidental state changes.
Next steps:
- Share your integration idea in the comments or request a sample repo template.
- Subscribe for a follow-up tutorial that walks through a complete code example and CI/CD pipeline for local integrations using Claude Computer Use API and coding with Claude Dispatch.
If you want, I can produce a starter repo template (TypeScript + Docker sandbox + Dispatch plan) tailored to your environment and the minimal command surface you need.